How to get Yourself Hacked on the Ethereum Network
We recently set up a transaction node connected to the Rinkeby Ethereum test network, for our server processes to execute smart contract transactions. Our morbid curiosity had gotten the better of us as we wondered what level of hacking existed against Ethereum nodes. The quickest way to get hacked, we postulated, involved:
- Give your transaction node a public IP with the
8545RPC port accessible to the internet. - On your transaction node, unlock your
eth.coinbaseaccount, having given yourself some Ether from the Ether faucet on Rinkeby ( https://www.rinkeby.io/#faucet ). - Expose all the rpc apis when you run
gethwith the“--rpcapi eth,web3,admin,debug,txpool,personal”flags.
We weren’t immediately hacked, but the hacks did come. In Figure 1 you can see 2 separate accounts hacking us in a 24-hour period. The “In” transactions are me topping up the account again from the faucet. The “Out” transactions greater than Ξ0 are the hacks. There are two separate individuals here transferring to wallets “0x0305702e2BbCE2d3D9e825fF707b40Dd0249a4cf” and “0x8A9c4d8649959c185ca2066dAA109600bcE53d13”.
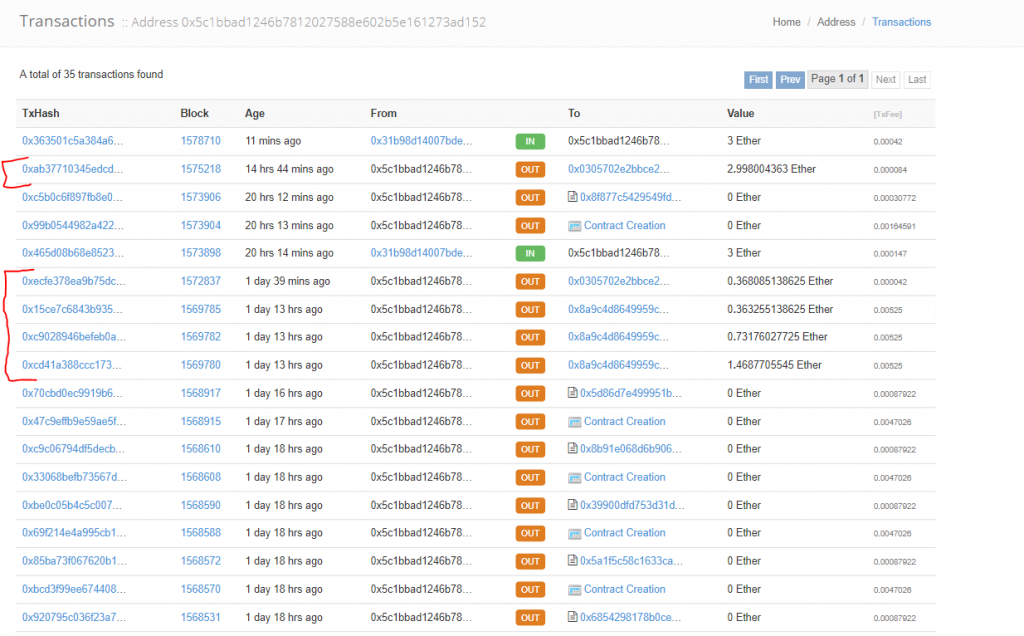
But why hack a test network? Well the answer, I suggest, is that these individuals thought they were stealing real Ether from a production node. When running RPC commands opportunistically against 8545 it is not obvious to the requester from the results that the operations are being performed on Rinkeby – at least not without further interrogation commands over RPC. In fact, when you query for these wallets on the production https://ethscan.io, you find both these wallets in use on the production Ethereum network, which confirms our hunch!
So:
- Don’t ever give your transaction node a public IP and close 8545 to the internet.
- Limit the amount of rpc apis enabled to the bare minimum.
- Don’t unlock your main Ether account on the transaction node. Have a separate wallet key that only stores the minimum amount of ether you need from day to day to fund your transaction fees.

